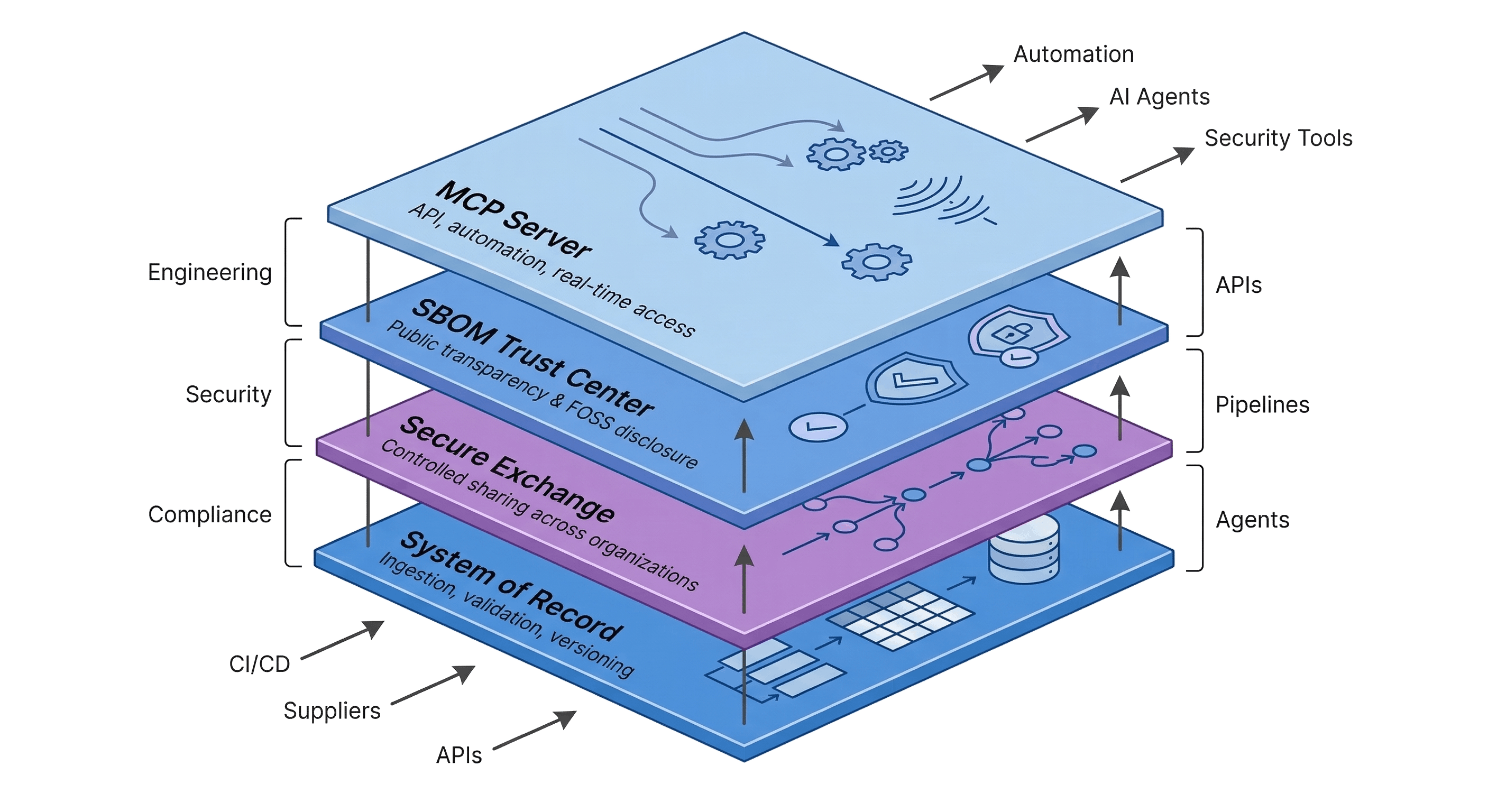
The system of record, exchange, and automation layer for SBOMs
Manage, share, and operationalize SBOMs across your entire software supply chain, from internal workflows to external transparency and automation.
System of Record
→Versioned SBOM foundation for ingestion, validation, and lifecycle tracking.
Secure Exchange
→Controlled SBOM sharing across suppliers, customers, and regulators.
SBOM Trust Center
→Automated public SBOM disclosure and FOSS transparency.
MCP Server (API & Automation)
→Real-time Software Supply Chain access for APIs, tools, and automated workflows.
Architecture
→Unified system connecting SBOM data, sharing, and system design.
Integrations
→Connect SBOM data with CI/CD, security, and compliance tools.
Solve software supply chain risk end to end
Engineering
→→ Automate SBOM workflows without slowing releases
Security
→→ Detect and respond to supply chain risk in real time
Compliance & Governance
→→ Maintain continuous compliance across all software
Supplier & Ecosystem
→→ Manage SBOM exchange across suppliers and partners
FOSS License Risk
→→ Eliminate license risk and automate disclosures
Try the platform. No setup required.
Analyze, assess, and operate your SBOMs in minutes.
No sales call. No integration work.
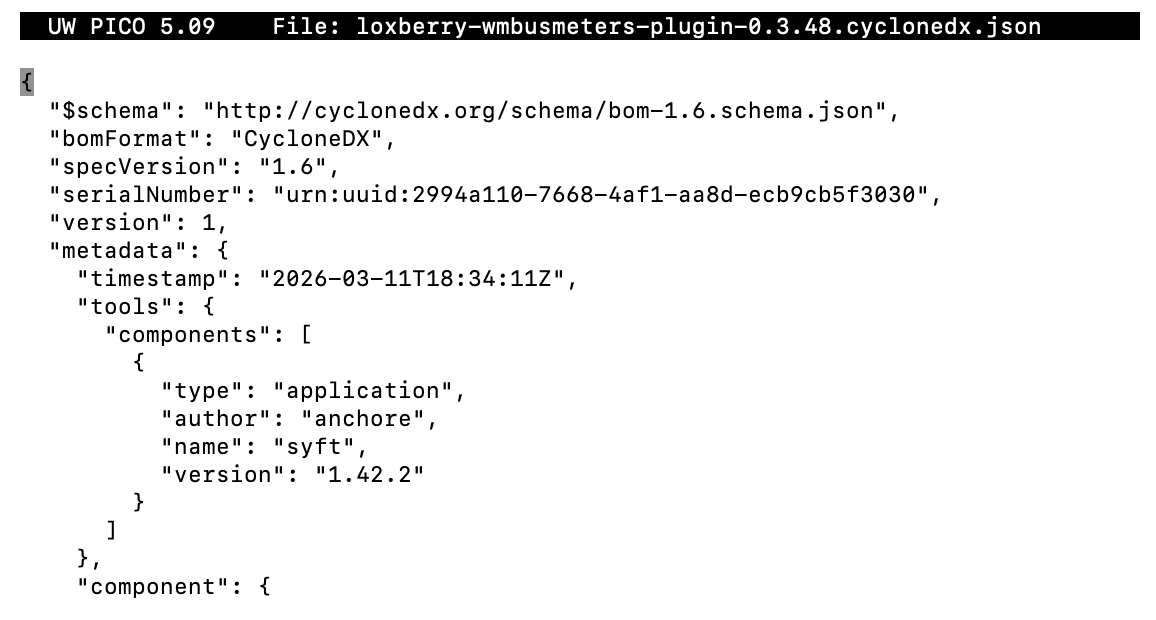
Free SBOM Scan
Instantly analyze your SBOM for vulnerabilities.
Analyze SBOM →Free CRA Assessment
Check your EU CRA readiness and identify compliance gaps before regulators do.
Check Readiness →Free SBOM Management
Manage SBOMs in a real system of record. Ingest, track, and validate for free.
Start Managing →Simple pricing. Built to scale.
Start with a free tier and grow into enterprise-grade SBOM operations, without changing your workflows.
Learn software supply chain security
Deep insights, practical guides, and regulatory clarity. Built for teams operating SBOMs at scale.
Blog / Insights
→Trends, best practices, and real-world SBOM strategies
Read Insights →SBOM Fundamentals
→Understand SBOMs, formats, and operational workflows
Learn SBOM Basics →SBOM Regulations
→Navigate CRA, DORA, EO 14028, and global requirements
Explore Regulations →Platform Datasheets
→Architecture, capabilities, and real-world workflows
Explore Datasheets →Building the future of software transparency
We’re creating the system of record for software supply chains, combining security, compliance, and trust.
About
→Our mission, vision, and approach to software transparency
About Exodos Labs →AI Lab
→AI-native SBOM intelligence and next-generation analysis
Explore AI Lab →Partner With Us
→Join our ecosystem and build together
Become a Partner →Events
→Meet us at conferences, webinars, and industry sessions
View Events →Contact
→Talk to our team about your use case
Get in Touch →